In my last post I talked about how one can use Azure Active Directory to manage user access for various resources. But it is not only users who need access to resources, there are times when your application code needs to access cloud resources. Your application might need access to key-vaults, databases, storage, etc. This can be managed in a similar manner we managed access for users using Managed Identities. Basically we give our application or resource an identity, and using the identity it can access any cloud resource like key-value just like a user.
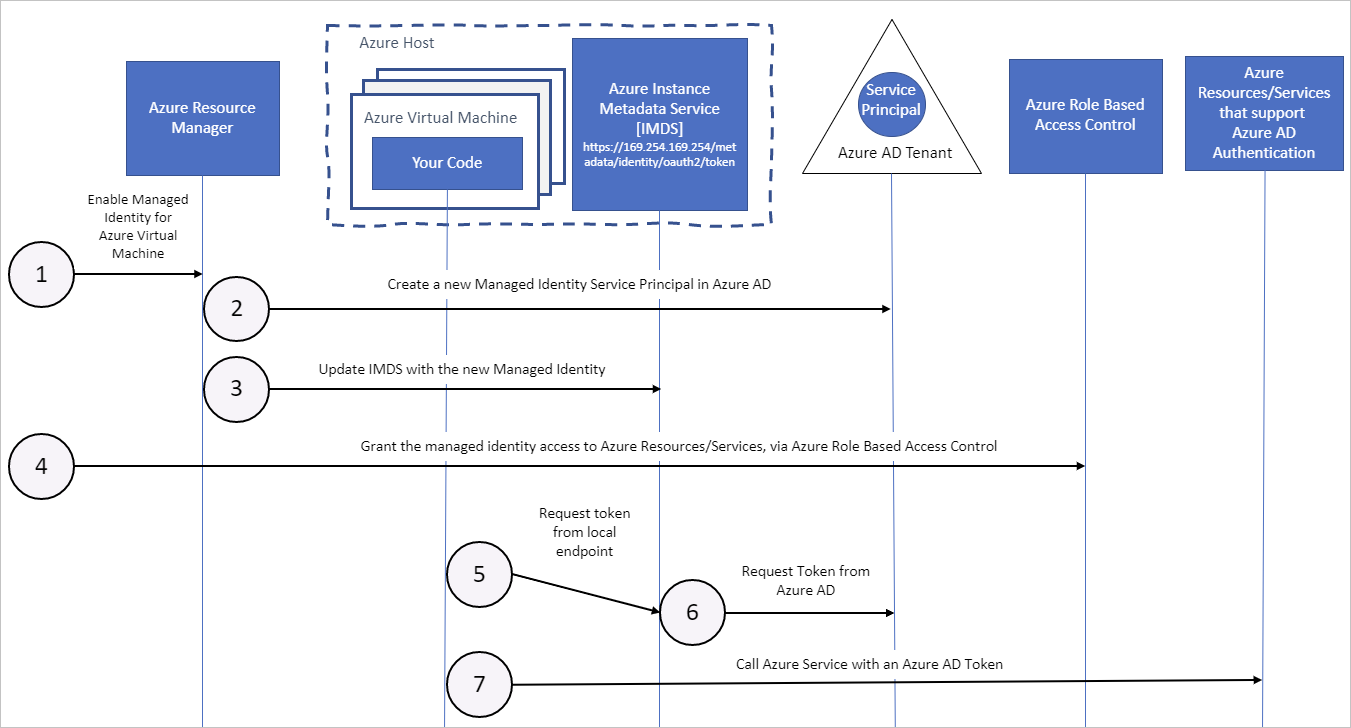
image source: https://docs.microsoft.com/en-us/azure/active-directory/managed-identities-azure-resources/overview
The image above shows how a resource with manage identity can get a token from Azure AD, and further use this token to access a cloud resource which gives permission to that identity.
Here is a video explaining the concept in detail
Here are a few key terms you need to understand
An “Identity” is a thing that can be authenticated.
A “Principal” is an identity acting with certain roles or claims.
A “Service Principal” is an identity that is used by a service or application. It can be assigned roles.
“Managed Identity” is an identity created for a service, which is like creating an account on Azure AD tenant. Azure infrastructure will automatically take care of authenticating the service and managing the account.